Chapter 6: Network Layer - cnacad.com.
Next Header: Protocol field copied from IPv4 header. If the value of the Protocol field is 1 (ICMPv4), then substitute it with 58 (ICMPv6). Reserved: 0 (all zero bits) Fragment Offset: Fragment Offset copied from the IPv4 header. M flag: More Fragments flag copied from the IPv4 header. Identification: The low-order 16 bits copied from the.
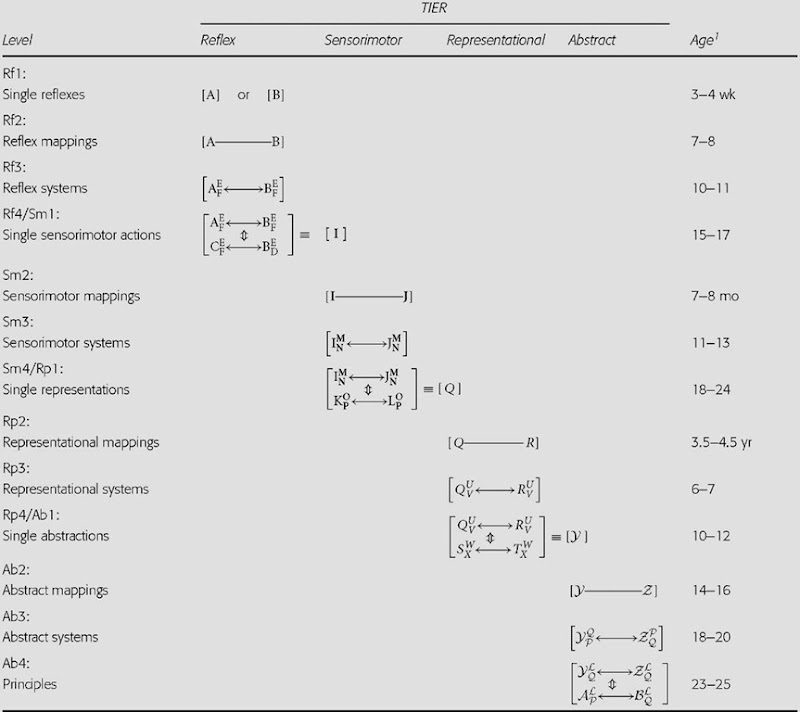
Options integrated in header fields Options supported with extensions headers (simpler header format) Figures 1 and 2 compare the header of a IPv4 packet and an IPv6 packet. Even if you don’t study packet header fields, you can see the difference between the IPv4 header (fragmentation fields are. italicized) and the “streamlined” IPv6.
Some differences are that it is stated that the IPv6 is more secure than the IPv4, the address size went from 32 bits in the IPv4 to 128 bits in the IPv6, extensible protocols are more flexible in the IPv6, IPv4 and IPv6 are not compatible, the IPv4 will not be able to support additional nodes or support for applications, and the threats are different for the IPv6 than the IPv4.
The current version is 4, and this version is referred to as IPv4. Length - A 4-bit field containing the length of the IP header in 32-bit increments. The minimum length of an IP header is 20 bytes, or five 32-bit increments. The maximum length of an IP header is 24 bytes, or six 32-bit increments.
IX) Protocol: 8 bit value used to indicate the type of protocol being used (TCP, UDP etc.). X) Header checksum: It is 16 bit value. It is used to indicate errors in the header only. Every node in the network has to check and re-insert a new checksum as the header changes at every node.
The field contains the IP protocol version. The current version is 4, sometimes called IPv4. Internet Header Length - IHL The header length is the number of 32-bit words in the header, including any options.
IPSec Encapsulating Security Payload (ESP) (Page 4 of 4) Encapsulating Security Payload Format. The format of the ESP sections and fields is described in Table 80 and shown in Figure 126.I have shown explicitly in each the encryption and authentication coverage of the fields, which will hopefully cause all that stuff I just wrote to make at least a bit more sense.